Welcome To Cloud Weavers – Products, Processes and Automation
Cloud Weavers Private Limited (CWPL), is a software product development company that specialises in Software Products and Solutions for a number of Industries. Our solutions use cutting edge technologies and is completely integrated with a multitude of new touch points like security and access control system, internet-of-things (IOT) and cloud solutions. At CWPL, we develop scalable software applications, business software and automation software. We develop and implement applications that automates everyday workflow and processes in your organisation and transform your organisation efficient and nimble.
- We cater to a number of industries.
- We understand the business of these industries.
- We provide total, integrated solutions.
You can be a Small-and-Medium-Enterprise (SME). You can be a small startup, in a remote corner of the world, trying to sell your fantastic product online, for the first time. You can be large, established organisation, who is frustrated with your current software providers, who provide inflexible, expensive and software that is not aligned with your organisation’s needs. We have solutions for you.
SMEs or startups, please look at the eCommerce Enablers, where we provide, simple easy-to-use, quick and practical solutions to cater to your immediate business needs. With our eCommerce Enablers, you can be up and running almost immediately.
For Large Organisations, we provide total solutions which helps you manage your entire organisation’s business and operations without with the needs to work with multiple vendors.We have immediate solutions for Golf and Country Clubs, Pre-schools, Food and Beverage outlets with Central Kitchen Operations… Name it.. we have it. Please click on Our Products to view the details.
About Us
Cloud Weavers Pte Ltd is a Asian company from Singapore, that was founded in August 2013. We fully understand the local requirements and needs of a Singapore client, but also that of Asian clients as well. We work with you on your needs and requirements in face-to-face meetings, and not just on the phone. Be it our Business Development Managers, Account Managers, Systems Analysts, Programmers, we will be there, with you, to understand and implement the solution according to your needs.
We have over the past 8 years, developed a number of solutions and products specifically for Small and Medium Enterprises (SME) and startup companies. We have ready-made, off-the-shelf products and solution for Golf and Country Clubs, for the Pre-Schools and Kindergartens, Construction companies and Subcontractors, Real Estate Companies and F&B restaurants.
Our Products
Cloud Weavers Private Limited is a premier software products development company and focuses mainly on development of SAAS products. We provide a complete range of operations automation products, specifically for Small and Medium Enterprises (SMEs) and Large Organisations. We have complete solutions for a number of industries – Golf & Country Clubs, Pre-Schools and Childcare Centres, Real Estate Companies. Our other products also include Learning Management Systems for Tuition Centres and Teaching Centres, and Central Kitchen operations for large Food & Beverage companies. We also have a complete set of software for Small and Medium Enterprises (SMEs) which is integrated to an SME’s business and operations. All these products are marketed under our brand name OnCloud.ai.
Products
- Club OnCloud
- SME OnCloud
- School OnCloud
- Realty OnCloud
- Learn OnCloud
- Marine OnCloud
- Kitchen onCloud
Club OnCloud
We are Golfers. We have waited on the sidelines to make a booking for a weekend slots to play a round of Golf with our buddies. We know the pain of waiting in queues to make a booking.
We are business people. We have worked with numerous clubs to understand the difficulties in managing the both the business and operations of a Golf and Country Club. We understand the value of customer satisfaction. We understand what is means to continually upgrade the club’s products and service to ensure that you remain a truly top club.
With all the understanding from a Club user’s and from a Club manager’s perspective, we have developed and implemented Club On Cloud. It is a premier product that provides all the features, functions and modules that are required run manage and run an entire Clubs frontend, backend, business and operations. The modularised but fully integrated Club On Cloud software has the following modules:

SME OnCloud
It is not easy if company and you are trying to compete on the same arena with Large Organisations. You would need a similar SME On Cloud is developed specially for Small and Medium organisations that need to manage the entire company’s sales, business and day-today operations. Functions that All the modules in our SME On Cloud work seamlessly with each other and bring efficiency and data sharing amongst the various functions of the Enterprise. SME On Cloud consists of the following, integrated modules.

School OnCloud
School OnCloud is an intelligent and practical solution to the tedious and laborious task of managing pre-schools. It is a comprehensive software that is a one-stop, integrated solution to all of your pre-school management needs.
School OnCloud provides a service that seamlessly integrates the 4 main pillars in any pre-school management system: Human Resource Management & Payroll, Customer Relations Management, Accounting Management and School Administration Management.
The vital tasks of managing front and back-end administrative processes, accounts, and all processes in between can be managed smoothly using the School OnCloud platform.
Realty OnCloud
Realty OnCloud is developed with one objective on mind: to make it easier for you to orchestrate and coordinate the numerous workflows managing the entire sales process in a complex clientele and regulatory environment in the Real Estate industry.
To properly market your business and listings into world connected world, the real estate professional need to manage their contacts, prospects and customers efficiently. This means it is of utmost importance to track what is important both to you and your customers. All information pertaining to your inventory of units that are for sale and rent must be intelligently integrated with the potential customer. You should be able to run mass mail and targeted campaigns and monitor the results effectively
Realty OnCloud is your perfect partner to achieve success in managing your Real Estate business.

Learn OnCloud
Learn OnCloud.ai is a Leaning Management Systems that is your perfect assistant in organising and scheduling course activities and preparing learning content can be really challenging. Learn OnCloud.ai gives you the ability to keep track of the students’ progress and ensure they meet their performance. It simplifies the tracking, recording, administration, documentation and the learning process.
For the students, the Learn OnCloud.ai provides students unlimited access to e-learning materials. Students can also access them through their tablets and smartphone. It is easy to integrate E-Learning with social media. Learn OnCloud.ai allows you to include links to social media such as Facebook, Twitter, and LinkedIn which can give extra benefits to your students.
Marine OnCloud
Marine & Offshore Engineering
One of the most diverse, manpower-intense, complex BUT the least automated industry is the Marine & Offshore Engineering industry. Marine OnCloud.ai custom-built solution for the Marine & Offshore Engineering industry. It caters to the specific needs of the Small and Medium Enterprises in this Industry.
The Marine OnCloud.ai provides ALL pertinent modules that is needed to run both the business and operations of the organisation. This includes an Account and Sales Management modules, Project Management modules, Workforce Management and Inventory Management. The Marine OnCloud.ai is a fully integrated system that would automate many of the manual and tedious process in the organisation.

Kitchen OnCloud
Kitchen OnCloud.ai Manage your chain of food outlets with our robust and simple Kitchen OnCloud.ai. Kitchen OnCloud.ai is Central Kitchen Management solution that keeps track of your operations and work procedure efficiently. With Kitchen OnCloud you would be able to track & manage orders, keep an eye on your inventory and track the delivery details, all at once.
Our solution was commission to launch Singapore’s (and probably Asia) first ever shared Central Kitchen that brought together 8 large competing restaurants to jointly operate and benefit from a shared Central Kitchen. It was indeed possible with Kitchen OnCloud.ai.
Kitchen OnCloud.ai is also a Cloud Kitchen system. With this, you would be complete run and manage on Online Ordering, POS, Inventory, Kitchen Display and Delivery Management.

Welcome to the NEW NORMAL. The Ezy Pzy NORMAL!
eCommerce Enablers

Covid-19 is a terrible thing. It has changed the way conduct our business. It has changed the way we speak to each other. It has changed the way we live. The world order has changed. Covid-19 has created a “NEW NORMAL”.
We, at Cloud Weavers are well prepared to handle the New Normal. We would also want you to be part of the journey to emerge victorious. We have put together numerous solutions – the eCommerce Enablers – called EzyPzy – for you to walk this journey successfully. The various solutions that we have for you are a start to the victorious journey. We want to you succeed in your business in this NEW NORMAL.
If you have
- No website
- or a Simple One Page website
- or a Completed website
Our solutions would enable you to start your eCommerce applications almost instantaneously! No complex programming, no need for IT personnel and no technical skills or knowledge is required. You have full control over your online business – like never before!
Your Business will be listed in your own personalised domain
pteltd.sg
Now, that is the NEW NORMAL!
eCommerce Enablers
- Auction Management
- Car Classified
- Car Rental/Leasing
- Class Scheduler
- Cleaning Business Management
- eCommerce Shopping
- Equipment Rental
- Food Catering
- Food Delivery
- Fund Raising
- Limousine Reservation
- Property Listing
- Restaurant Reservation
- Saloons/Spa Appointment
-
Auction Management
If you have antiques, interesting products, or just products you know would of interest to many buyers, then putting these items on an item would be the best way to get value for your products. Let your clients place bids for all products you are selling on your website! Add countless categories, products, and attention-grabbing descriptions and image galleries. Specify each bid’s closing time and automate account registration confirmations. Send notifications to admins and bidders and manage your real-time bidding process with ease! Clients can keep track of their bids and update their profiles online. You have full control of your Auctions using our Auction Management solution.
-
Car Classified
Are you a used car company? Are you having difficulties getting customers to visit your showroom? Is placing your cars on sale in generic car classified website lost amongst the many cars that are for sale in the website? Then, it is about time you have a your individual presence, listing just your own cars. Build your own brand. Keep details of customer and their interests in your own built-in CRM. Have full control, through our Car Classified solution.
-
Car Rental/Leasing
If you have a fleet of vehicles or a few vehicles, then here is a way to manage your business very easily, with our CarWith the recent pandemic, taking public transport can be a hassle. There could also be a group of people who prefer to not to take public transport for a variety of reasons. The alternative to these people are is to Rent a car short term or Lease a car, long term. If you have a fleet then the Car Rental/Leasing is the solution for you. You have full control on the managing your rental rates, which vehicle you want to rent or lease out and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
Class Scheduler
You are a tutor. You get innovative in conducting classes during the pandemic period. You can use one of the many sessions of the classes, and you manage you students and their registration for the classes through a spreadsheet today or in the traditional paper and pen. With the Class Scheduler, you can put up your classes, register students for each of the class and track who is accessing your classes. You can even include payment for classes if you need it. You have full control on the managing your classes, set a limit on the number of people who can register for the classes, set prices and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.
-
Cleaning Business Management
If you are running a small cleaning business or you are an individual we wants to manage personalised services for home or office cleaning, then our smart and user-friendly enquiry Cleaning Business Management solution will provide you with all the functions and features the you require to bring your business online! You can set an hourly rate for your cleaning services, describe your standard cleaning package, and offer additional services charged depending on the time needed, set prices and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
eCommerce Shopping
Everyone is thinking about it, many are talking about it, but few have done it! Bringing the business online and going full swing may look like a daunting task. Yes, it can be. But with our eCommerce Shopping solution, you can setup your customised and personalised eCommerce shop, get online and start receiving your orders and collect payment in a matter of days – not weeks or months. You can set individual item price, stock availability, delivery charges, customised photos, additional services like gift wrapping etc and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
Equipment Rental
Just like vehicle or car rental, you can use our Equipment Rental solution to manage your own e-commerce platform for renting all kinds of equipment – from tools, outdoor equipment, sports equipment, construction tools etc. You can set an hourly rate or long term rentals, describe your various equipment with photographs, and offer additional services charged depending on the time needed, set prices and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
Food Catering
Home-based business is a big growing sector – more so now! With our Food Catering solutions, you would be able to have an almost immediate, well-organized online menu and enable customers to pre-order your exquisite meals and drinks online. You could offer them different kinds of packages as per occasion – breakfast, corporate cocktail, wedding, birthday party, etc. You would be able to add as many products and categories as you wish, manage orders, process payments. Clients only have to make their choice, select their preferred payment method and wait for their delivery!

-
Food Delivery
Are you mid-sized restaurant, a small restaurant, a hawker – it does not matter. With our food order and delivery solution, you will be able to or create your restaurant menu, manage categories, orders, pick-up and delivery, payment options and vouchers. The choice of whether you use your own delivery channel or get the customers to pick-up their own delivery is fully within your control. You can set different prices for different food items and sizes, price for additional items like cutlery or additional sauce and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
Fund Raising
In addition to using publicly available fund raising websites, you also streamline your fundraiser campaigns with our Fund Raising solution. You can publicise and popularise your cause through the Internet to get a higher public response. Visitors to your side can donate to your cause using any of the available ways to process transactions – PayPal, bank account, PayNow or PayLah. Set up your campaigns with ease and engage more people in your charity project.
-
Limousine Reservation
If you provide or plan to provide premium car reservation service for fixed periods, airports pickups or drop-off, or bring your customers for tours around Singapore, then the Limo Reservation solution would work best for you. You can add as many limousines and extras – like flowers to champagne to tour guide etcand offer different transfers and city tours. You can set an hourly rate or specific periods describe your various limos with photographs, set prices and see your bookings, revenues and customer-related information in a beautiful, easy to understand dashboard.

-
Property Listing
Calling all Property Agents! Are you listings of your beautiful properties getting lost in major listing websites? Do you have to pay much for getting your listing, even to be listed? Well, then you would love our Property Listing solution. It is simple, easy to use and does not take up too much of your time. You can list properties for sale and for rent, edit property details, add multiple images, publish classified ads online, create users and assign roles. You can have your own branding and not get lost in the 1000s of listings.

-
Restaurant Reservation
Are you depending on a third party reservation system to take your orders and booking for your restaurant? Are you paying a hefty fee whenever a reservation is done? Why not manage your own reservation or a self-service reservation by the customer, all in your website? Our Restaurant Reservation solution is a convenient self-service table booking system that can be embedded on your restaurant website. With the restaurant reservation system, you can customize the booking process, enable people to book a table through your site, manage restaurant availability, and reservations. Take control of you reservation immediately.

-
Saloons/Spa Appointment
Do you own a beauty saloon, hair saloon, a Spa or are you a budding hair stylist working from home? Do you want to be able to manage the services offered and the bookings made? Would it not be fantastic if you can have beauty or hair treatment or facial treatment packages that can use be completely managed by you? Our Saloons and Spa Appointments booking solution allows your customers to make appointments online very easily. You would be manage appointment calendars, individual schedules, services, and rates. In addition our intuitive dashboard provides you with a complete views of your revenues, customers, appointments and services.

Our Services
Cloud Weavers Private Limited provides specialized information technology and software consulting services to its clients globally. Our expert team of business analysts, application developers, web designers, quality assurance professionals and online marketing experts has accomplished the developments of a large number of projects for global clientele. Whether it is an e-commerce platform or online forums, we have done it all. We integrate the latest technologies and trends into our services. Cloud Weavers Private Limited has a large team of experience and skilled designers, developers and project managers with the technological expertise equipped to design, develop and implement the solution of any complexity.
Services
- Business Consulting
- Software-as-a-Service
- Software Product Development
-
Business Consulting
Our Business Consulting group delivers solutions to a broad spectrum of marketing and sales challenges. We help our clients transform their marketing and sales organizations by implementing solutions based on rigorous research and analysis underpinned by thoughtful leadership.
Data Analytics Consulting
The use of social, mobile, analytics and cloud technologies is already enabling our advanced analytics solutions to extract meaning from your data so you can refine the products, services and experiences required to outperform your competition. Whether through analytical models, systems integration or data analytics and strategic consulting, we can help your data drive experience.
Supply Chain Consulting
Our end-to-end supply chain expertise across policy, process and technology issues enables us to tailor solutions to meet your market needs. The result is reduced cost to serve, optimized inventory working capital and fast response to demand changes.
IT Strategy Consulting
In today’s increasingly virtualized and globalised workplace, organizations need new ways to innovate, allocate resources and reinvent processes leveraging the latest trends. That’s where smart strategies pay off, particularly in times of economic uncertainty. Working closely with clients, our consultants help your company define new innovative target operating models to drive the business transformations needed to achieve success.
-
Software-as-a-Service
Many traditional IT companies are increasingly under pressure from customers to deliver their offerings in a Software as a Service (SaaS) delivery model. Our SaaS development services offer a proven track record of helping such organizations make a transition or augment their offerings with SaaS solutions. Our experienced SaaS architects and developers have helped successfully conceptualized, developed, deployed and managed several new SaaS solutions.
Our SaaS Development Services can help you with:
- SaaS Strategy Conceptualization
- SaaS Platform Strategy
- SaaS User Experience Design and Prototyping
- SaaS Architecture Design
- SaaS Development Testing
- On-Premise to SaaS Migration
-
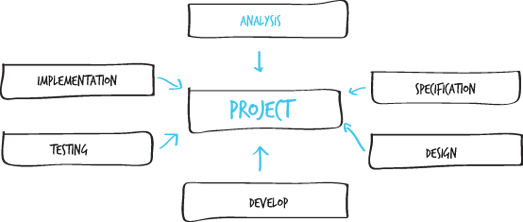
Software Product Development
Changing dynamics in industry, business and technology landscapes create opportunities for new software solutions. Bringing these solutions to the market in an accelerated manner provides an early mover advantage and avoids wasting time and unnecessary spend in playing catch up.
We have a proven track record of working with software technology organizations to successfully introduce over 150 new software solutions over the last 14 years. We are constantly evolving our capabilities to help software technology companies do more with less: deliver software solutions on popular and trending platforms faster and ensure high quality within time constraints, with fewer resources, and lower costs. We achieve this by deploying best-in-class resources, adopting and standardizing best practices and best-in-class development tools, and leveraging development accelerators as often as possible.
Contact Us
If need any info please contact us!
Head office address:
Cloud Weavers Pte Ltd, 10, Kaki Bukit Ave 4,
#06-63 Premier@Kaki Bukit, Singapore, 415874
Mail for information:
info@cloudweavers.sg
Call for help:
+65 8879 0088
Please fill up the form and send your queries to us: